What Is Context Engineering?
Context Engineering: The Next Evolution Beyond Prompt Engineering
Context Engineering is the discipline of designing, structuring, and managing the entire context window (system prompt, RAG, tools, memory, metadata), not just the prompt. Think of it as creating a workspace and engineering what flows into it: e.g., system instructions, tool definitions, retrieved documents, memory, prior conversations, user metadata, and structured data.
Context Engineering builds the entire information environment in which an AI Agent operates.
Context Engineering vs. Prompt Engineering
The two terms are often used interchangeably — they shouldn't be. They operate at fundamentally different layers of the AI stack.
Prompt Engineering crafts the input . It optimizes the wording of a single instruction sent to a model.
Context Engineering architects the environment. It governs everything the model sees at inference: the system prompt, retrieved documents, tool definitions, prior turns, long-term memory, user metadata, and the guardrails around all of it.
Here is an Analogy: Prompt Engineering is writing a sharp question for a brilliant consultant. Context Engineering is making sure that the consultant has the right files on the desk, the right tools at hand, the right history in mind, and the right rules of engagement — before you ask the question.
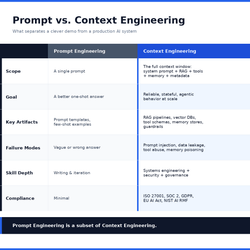
Prompt Engineering is a subset of Context Engineering. In short: Prompt Engineering crafts a question. Context Engineering builds the entire information environment around that question.
Who Should Learn Context Engineering?
AI Engineers & Architects - Building agentic systems
vCISO & Security Engineers - Designing AI-powered SOC, detection, or compliance agents
SaaS/AaaS Product Teams - Embedding LLMs into customer-facing features
vCISO & Privacy Officers - Governing AI data classification and handling
DevOps/MLOps - Responsible for AI deployment pipelines
If your product retrieves, remembers, or acts on behalf of a user, you need Context Engineering
Two Real-World Applications
Example 1: Cybersecurity AI Agent for a SaaS Company
A Tier-1 SOC Analyst agent must triage alerts from a SIEM. Context Engineering provides:
Retrieved context: the specific alert, related logs (last 24h), asset criticality, known false-positive patterns
Policy context: ISO 27001 incident classification rules, SOC 2 evidence requirements
Tool context: Schemas for ticketing (Jira), isolation (EDR), and notification (Slack)
Memory: Prior decisions on similar alerts for the same tenant
Result: the agent escalates accurately, cites controls, and produces audit-ready evidence — without retraining the model.
Example 2: Privacy-Aware Customer Support Agent for an AaaS Platform
A Customer Support agent answers questions about a customer's analytics data. Context Engineering enforces:
Tenant isolation: Retrieval scoped to the authenticated customer's namespace only
Data minimization (GDPR Art. 5): PII redacted before entering context
Jurisdiction routing: EU customer queries restricted to EU-hosted models
Auditability: Every context assembly logged for DPIA review
Result: Compliant personalization without cross-tenant data leakage.
Security Risks & Compliance Issues
Security Risks
Prompt Injection — malicious instructions hidden in retrieved documents or tool outputs hijack the agent.
Context Leakage — Sensitive data from one tenant or session bleeds into another.
Sensitive Data Exposur — Secrets, PII, or PHI inadvertently pulled into context.
Tool Abuse — Over-permissioned tools invoked from a poisoned context.
Memory Poisoning — Long-term memory stores corrupted by adversarial inputs.
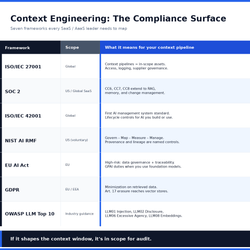
Regulatory & Compliance Considerations
Context Engineering - Security Controls & Governance
Security
Threat Modeling for LLM Systems (STRIDE adapted, OWASP LLM Top 10)
Data Classification and Tagging
Identity, tenancy, and access control patterns
Input/output filtering and guardrails
Governance
Privacy-by-Design and DPIA Execution
AI risk management (NIST AI RMF, ISO/IEC 42001)
Evidence collection for audits (SOC 2, ISO 27001)
Next Steps
Audit your current AI features — map every source feeding the context window.
Threat-model the pipeline against OWASP LLM Top 10.
Instrument logging and tracing before scaling.
Codify context assembly rules as policy-as-code.
Align with ISO 27001, ISO 42001, SOC 2, and the EU AI Act from day one — retrofitting is expensive.
Consult an AI-Native vCISO to ensure your Context, AI Agentic Workflows and Deployments are safe, secure and meet regulatory requirements.
Prompt Engineering got us talking to models. Context Engineering is what lets us trust them in production.
Let's turn your Manual Business Processes into AI Agentic Workflows.......Learn More
Our Industry Certifications
Our diverse industry experience and expertise in AI, Cybersecurity & Information Risk Management, Data Governance, Privacy and Data Protection Regulatory Compliance is endorsed by leading educational and industry certifications for the quality, value and cost-effective products and services we deliver to our clients.